by Business Analysis (BAPL).
Recently my partner’s daughter (Lucy) said she had an invitation to a gender reveal party. Unfortunately, I come from a day long gone when gender reveal parties didn’t actually occur. Instead it was a surprise when the baby was born, and we took what came enjoying or commiserating with our friends and families. After much conversation and deliberation, I was informed that a gender reveal party is simply an excuse to celebrate the new baby before it was born instead of having to wait until the day. If only we could have so much fun in the digital world?
In the digital world we are all gender neutral and there are no “surprises”. Just think that we never have to guess what colour baby clothes or colour laptop covers we would need to buy.
However, on reflection that isn’t quite true. It is not unusual that we provide gender information when registering a new account online or within an organisation, and certainly the HR department are aware and identify our gender. This leads me to introduce the process for registering a new account because it is here that we inform the company of our specific details for access.
Before we can do anything with an identity, we need to capture the information required to create a digital representation of ourselves. Identity Management builds the relationship we have with specific applications by using our personal details. Items such as the position held, our location and even gender (yay it’s a girl!) matter in determining whether access is provided to specific applications and the level of authorisation that is provided. It’s not just about providing access to barbie dolls for girls or matchbox cars to boys although it could be if the business rules were to be that specific.
Identity Management builds the relationships we need with applications by associating specific attributes of the identity to the application. These associations are defined through business rules. For example, one business rule may dictate that an identity with a position attribute of manager may be provisioned with access to the finance system as a manager profile allowing the user to approve expense claims and authorise purchase orders to a specific value.
These details are captured in the registration process. Almost all environments, including Facebook, Google or Yahoo, will follow this process in creating a new account. I call this the registration process (for customers) keeping in mind that in a company, a new staff member will be created by the HR department.
The data captured in the registration process establishes the identity. The business rules consume the identity data to determine the access to applications and resources that require provisioning.
In corporate organisations, the initial account is created by HR as the department responsible for all staff and temporary personnel. The registration process is typically one that is used by consumers in registering an account to access specific applications or services.
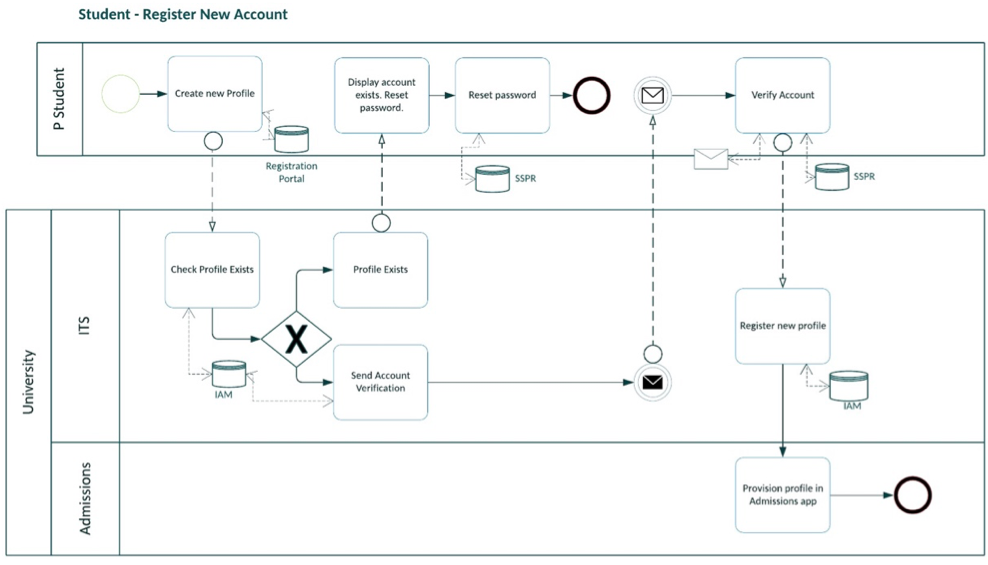
The following BPMN diagram outlines a typical registration process.
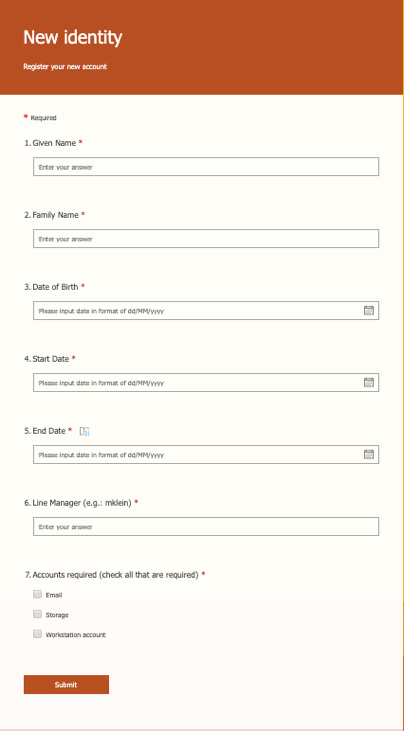
The registration form should be kept short and capture the minimal information required to service the customers initial provisioning requirements. Once the registration is complete, the business rules may require that further information is provided to access additional data or applications. I tend to request simple fields be completed so that an account can be created and a password set by the customer through a verification email or SMS.
These fields may include:
- Given Name (use given name rather than first name as many nationalities use the given name as the last name)
- Family Name (once again using family name instead of surname as some nationalities are confused with surname.)
- Date of Birth. (using the date of birth along with given and family name attributes will allow checking whether the account already exists. Typically these three fields will have a 95% success rate of identifying the individual. i.e. typically there is a 95% chance that a match of given name, family name and date of birth will be the same person as previously registered.)
- Personal email address (This will be required to send the verification email to verify the account.
- Phone number (This is optional but I put it in as an alternative to sending a verification email this may be used to verify the account via SMS.)
- Country (It is good to capture location somehow. Depending on the business type this is more or less relevant. If operating as a regional council this location may be a post code rather than country.)
Optional fields may be added including:
- A drop down box to select an application or resource required. (This allows immediate provisioning once the account is verified.)
- Opt in / opt out for email newsletters etc.
- Start date / End date. (I use a start and end date fields for short term temporary accounts only. Providing this to customers would not be relevant as the customer would simply set it for 50 years or so.)
- In some instances, it may be suitable to have a short questionnaire as this may be used to provision certain interest groups for newsletter notifications.
- Line Manager. This field would also be used in creating a temporary personnel account for a company. Setting the line manager identifies the approver who would approve the account creation. This would be in lieu of sending a verification email for the password as the new identity can set the password on first use of the account. A temporary password may be set or Multi factor authentication be setup to ensure security is maintained.
- and gender.
The following form is an example I created on Microsoft forms.
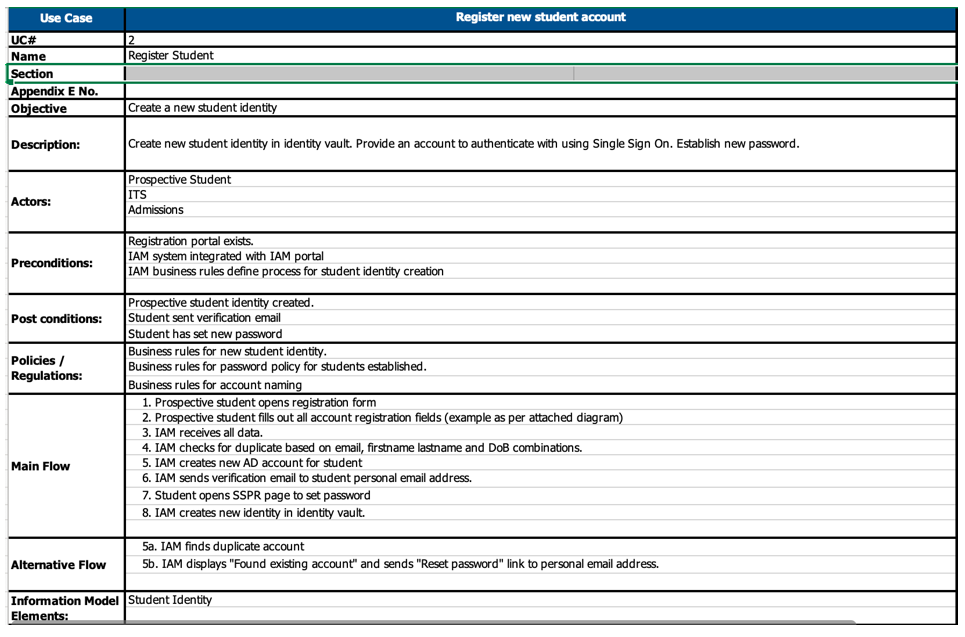
Once the identity data is captured, the IAM system would confirm that the account with these details does not already exist. Typically the IAM system will use the given name, family name and date of birth to check for duplicate accounts. If this is a new account the IAM system will create it using the details provided. If an account with these details already exists it may present this to the customer asking whether the existing account is the same person and typically sending an email to the registered email address to verify the new details and connect this account.
Once the account name is established, an email with a verification button may be sent to the personal email address. This usually involves the customer clicking on the link / button in the email and setting the initial password for the account.
The following image provides the use case I have used to register a new student account.
Registering a new account correctly is critical for organisations. It is imperative that the registration process is simple and concise yet captures the data the company requires to provide opportunities for marketing and to deliver the services requested by the customer. In many cases, organisations are registering new accounts by allowing customers to use their social media accounts such as Facebook or Google, Yahoo or any others. However, many customers are reluctant to provide their details using social media as the protocol (OAUTH) used to do this allows the web site to capture a lot more than just name, gender and date of birth. As such, privacy issues become a major concern with customers. The Privacy act of 1988 (Australia) and GDPR (EU 2016) places the risk on the company to protect personal data with heavy fines and compensation (Google was fined EU$50 million in 2018 for breaching GDPR rules) if private data is accessed and released by unauthorised people
In the Identity environment there is such a thing as “too much information”. But providing the right access to applications and resources requires the right amount of information to be captured. It’s a fine line between minimising the information requested and ensuring individual access is provided. Maybe we do need to consider the gender in the registration process which may see us celebrating each new account as a boy or girl yet. At least this would make Lucy happy.